Android has been on the market since 2008, and this year 2018 marks a decade of dominance in the world of mobile platforms. As part of being dominant in the mobile computing market comes the reciprocal risk of being targeted by cybercriminals. Android, due to its open platform nature enables users the capability to install apps outside the official Google Play Store. This flexibility is both an advantage and disadvantage of the Google mobile OS, compared to the strict walled garden policy that Apple implements for its counterpart IOS devices.
Users start to enter the risky areas of Android usage the moment they desire to acquire paid-apps without paying for them. Threat actors inside the mobile community have devised ways to infect an Android device through paid-apps side-loaded as a free APK download. Sideloading is the process of installing an Android app outside a Play Store, the app is distributed as .apk files. This .apk file format has similar functionality in Android as the setup.exe program installer in Windows. It installs the app to the device without the vetting process initiated by the Play Store.
This bypasses the very protection provided through defaulting the installation of apps strictly from the Google Play Store, also known as “Verify Apps” functionality: Below is a sample image of Verify Apps blocking an app from installing: Worldwide, millions of users have been downloading APK installers from questionable places on the internet instead of the Google Play Store. Mostly in order to bypass the copy protection of the apps, which cannot be done if the program is downloaded through the Play Store.
Worldwide, millions of users have been downloading APK installers from questionable places on the internet instead of the Google Play Store. Mostly in order to bypass the copy protection of the apps, which cannot be done if the program is downloaded through the Play Store.
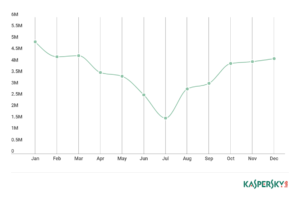
In 2017, Kaspersky, a Russian-based Antivirus vendor detected more than 5 million instances of malicious app installation. The 2017 data revealed in the below diagram from https://securelist.com/mobile-malware-review-2017/84139/. The instances of virus infection in Android are not seen to decline any time soon.
Malware penetration is very prevalent in Asia and Africa, two continents with the least penetration of Google’s Online Services. These facts stem from the desire to acquire paid-apps for free, which is happening more frequently in Asia and Africa than the rest of the world. The popularity of the Android mobile platform encouraged more malware writers to enter the mobile world, and also which motivates antivirus companies to port their branded desktop antivirus software as an Android app. As the new AV Industry in Android is taking a hold of some market share, Google itself took the responsibility of securing their mobile OS by embedding a pseudo-antimalware scanner bundled with the Google Play Services itself, the Google Play Protect.
The popularity of the Android mobile platform encouraged more malware writers to enter the mobile world, and also which motivates antivirus companies to port their branded desktop antivirus software as an Android app. As the new AV Industry in Android is taking a hold of some market share, Google itself took the responsibility of securing their mobile OS by embedding a pseudo-antimalware scanner bundled with the Google Play Services itself, the Google Play Protect.
Below are the 5 Well Known Android Security Apps vying for market share in the new Android Antimalware scene:
1. 360 Security
2. Avast Mobile Security
3. McAfee Mobile Security and Lock
4. Norton Security and AntiVirus
5. Security Master
Similar to their desktop PC counterparts, the 3rd-party Android antimalware apps are not just plain malicious software scanners. They are suites in their own right, with features that are not even related to being an antimalware product such as:
1. Wi-Fi monitor and vulnerability scan
2. App locking capability
3. Remote Wiping
4. Photo vault (password protect images folder)
5. Thief selfie
6. Junk cleaner
7. CPU boosting
This collection of features may make or break the effectiveness of the antivirus app, as Android users suffer from bloatware more than a desktop or laptop PC users, as a smart device has fewer system resources. An Android user that is only looking for automatic scanning of malicious apps and automatic removal is receiving more than what they signed-up for. This may be favorable or unfavorable to the Android users depending on preferences, those that prefer the minimalist view will just settle for what Google has to offer by default, Google Play Protect.
Google Play Protect is installed to all supported Android Device, starting with Android Ice Cream Sandwich (version 4.0). It is a non-removable module of the Google Play Services, that is installed by default in all certified Android Device. A certified Android device is an Android Device with a bundled Google Apps, mobile device manufacturers pay Google a licensing fee to install it to the devices they sell to the public. Only custom ROMs from external developers do not come with Google Apps bundle, which means almost all mainstream Android devices for sale in the market comes with Google Play Protect.
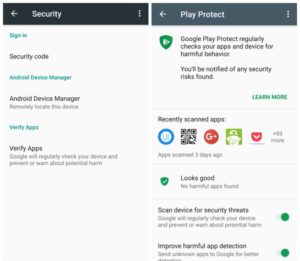
The advantage of just letting Google itself to secure Android is practical. The mobile user doesn’t need to do anything to keep the system running securely, as Google Play Protect cannot be uninstalled by anyone without root access to the phone or tablet. Like the third-party antivirus apps, it scans the device for known harmful apps and security threats that Google discovers and removes them automatically. Unlike the competition, Google Play Protect is free to use and it is not crippled in any way compared to the commercial offers from the above-mentioned 3rd-party antivirus vendors.
Related Resources:
LokiBot, The Android Malware Problem Since 2016
With FIDO2, Android Looks To Leave Password Behind
